FEATURED POST
Cyber Presilience® – The Human-Centric Approach to Cyber Security
The ground-breaking concept called Cyber Presilience® takes a human-centric approach to cybersecurity. By integrating people, processes, and technology, Cyber Presilience® aims to build a robust cybersecurity defence strategy tailored to each organisation’s unique needs.
Unpacking the CrowdStrike Outage: Business Continuity and Human Factors
Unpacking the CrowdStrike Outage: Business Continuity and Human Factors Events - Risk 2 Solution Group | Published 26 July 2024
“Unpacking Safety and Security Insights from the Attempted Trump Assassination” Webinar
Webinar Recap: "Unpacking Safety and Security Insights from the Attempted Trump Assassination" Events - Risk 2 Solution Group | Published
SoCI 2024 – Where to From Here?
Thank you for joining us for the "SoCI 2024: Where to From Here?" webinar. It was a pleasure to host
Ensuring Critical Infrastructure Cyber security by August 2024 – What Are Our Chances?
Making Risk and Security Work for You and Your Organisation – Turn Risk to Opportunity
Written by Dr Gavriel (Gav) Schneider CCRO, CPP, FISRM, ChFInstP. The need to protect and secure assets, information and people is not a new
Embedding a Learning Culture in Your Organisation
“Every enterprise is a learning and teaching institution. Training and development must be built into it on all levels—training and development that never stops.” —
Emergency Management Planning Services
PRESS RELEASE Emergency Management Planning Services We are excited to advise that Risk 2 Solution Pty Ltd (R2S) has acquired a new
Beyond Resilience: The Essential Role of Presilience CISO Services in Fortifying SMEs Against Cyber Threats
In the current digital era, the stakes for businesses, especially small to mid-sized enterprises (SMEs) in Australia, have never been higher when it comes
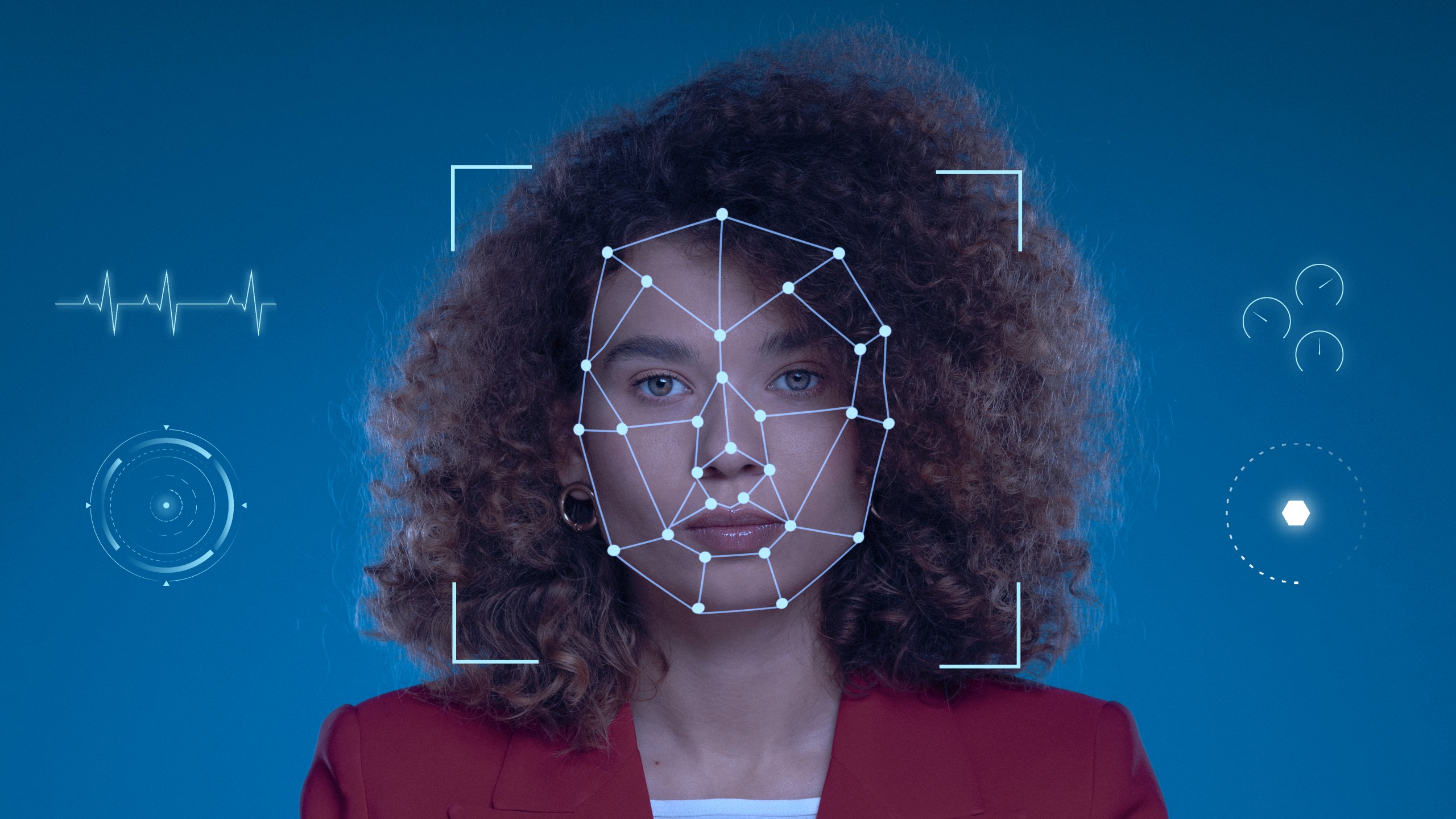
Cyber Presilience® – The Human-Centric Approach to Cyber Security
An engaged workforce is undoubtedly the strongest layer in a cyber defence strategy. In the battle of usability vs security, usability will always win, unless the individual 'why' is connected to the organisational 'why'.
Critical Infrastructure is Under Attack from Hackers
Why a 'wait and see' approach may prove disastrous for Australia. Earlier this month, Australian security researcher Sick Codes hacked a John Deere 4240 display and installed the vintage 1990s video game DOOM.